A secure encrypted cloud solution is essential for every company, but many are not exactly aware of what the different encryption methods involve or what they specifically mean.
Encryption generally refers to a process that converts plaintext into unreadable characters using a key. With the help of the key, the encrypted text can be decrypted again.
More and more data is being processed, stored, and transmitted digitally, which is why the need for secure encryption is increasing at the same time. The risks of data loss or misuse are well known.
This article aims to describe common methods in more detail and illustrate them using various examples.
In general, there are various forms of encryption technologies. These include:
1. Symmetric encryption
2. Asymmetric encryption
3. Hybrid encryption
Accordingly, there are various methods that apply these forms of encryption.
Symmetric encryption
= also referred to as “secret-key cryptography”
In symmetric encryption, only one key is required for both encryption and decryption. Therefore, the key must be known to both the sender and the recipient.
The advantages are that the method is considered simple and the exchange of the message is fast.

Disadvantages
Since the exchange of the key should take place confidentially, this creates the key exchange problem. A secure way must be found to exchange the key without interception. The safest method would be a personal meeting, which is often not possible in practice.
If multiple messages are to be sent to different participants, the number of keys increases rapidly.
Asymmetric encryption
= also referred to as “public-key cryptography”
Asymmetric encryption requires two keys. The key used for encryption is public and accessible to everyone, while the second key used for decryption is private.
Asymmetric encryption has the advantage of being a method that offers a high level of security and cannot easily be broken by attackers. This method can also bypass the key exchange problem or be used to create digital signatures for authentication.
More about digital signatures can be found in the section that discusses the RSA method.
Example
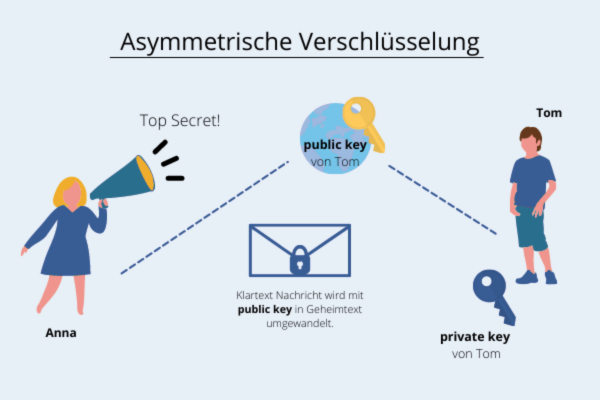
Asymmetric encryption
Assuming Anna wants to send Tom a secret message.
For the exchange, Tom must first generate a key pair. So that Anna can encrypt the plaintext message, she needs Tom’s public key, which is fortunately public and therefore does not need to be communicated secretly.
With the public key, Anna can now encrypt the message for Tom, and he can then decrypt it with his private key.
Disadvantages
Despite the high level of security this method provides, it is very computationally intensive and complex, especially when large amounts of data need to be encrypted.
As a result, the method is also much slower than symmetric encryption.
As a solution, hybrid encryption is therefore recommended.
Hybrid encryption
Hybrid encryption is a combination of both methods. For example, a symmetric key is exchanged using the asymmetric method, so that the actual communication takes place symmetrically.
This not only avoids the computationally intensive and slow asymmetric method, but also bypasses the key exchange problem.
Key pairs can, for example, be generated using the Diffie-Hellman method. This method is based on mathematical calculations and information exchanged between the communication partners.

Learn more about the encryption of leitzcloud on our website.
RSA method
The name RSA is derived from the initials of the mathematicians who discovered the method. It is one of the most widely used asymmetric methods, used for encryption and the creation of digital signatures.
RSA has the property that plaintext letters do not always correspond to the same ciphertext letters. In addition, it consists of a key pair—the private key cannot be derived from the public key. This method is therefore considered secure, as there is currently no algorithm that can factor a number larger than 789 bits into its prime factors. Modern RSA encryption therefore has a minimum key length of 3072 bits.
To decrypt an RSA system, additional information is required, which is only contained in the private key.
The private key is based on a one-way function, meaning the function is easy to compute but cannot be reversed. With the required additional information, however, the inversion can be performed easily.
Excursion
RSA signatures
As mentioned at the beginning, the RSA method can be used to create a digital signature that serves to authenticate the sender.
Unlike asymmetric encryption, the sender creates the digital signature of the message using their private key, allowing the recipient to verify the digital signature with the public key. A distinction can be made between a universal and a non-universal signature.
| Non-universal signature | Universal signature |
| A signature is created with the private key and attached to the transmitted message. If a third party intercepts the communication channel, they can also verify the sender’s authentication.* | The digital signature is additionally encrypted with the recipient’s public key, so that only the recipient can verify the sender’s authenticity. |
*The authenticity of the sender does not necessarily need to be kept confidential at this point.
SSL and TLS
SSL is the abbreviation for “Secure Sockets Layer” and describes the layers used by the encryption protocol during data exchange between two computers. Communication between them is encrypted and therefore protects against access by third parties.
The main task of SSL is to give the web user the assurance that they are communicating securely with the server and to secure the HTTP protocol (Hypertext Transfer Protocol). The URL is displayed as HTTPS when the website is protected by an SSL certificate. It can also be recognized by a padlock icon in the URL bar or by it loading in green.
TLS (“Transport Layer Security”) is the more modern version of SSL, offering higher security. Since SSL is still much more widely known than TLS today, it is often still referred to as SSL, or the combined term SSL/TLS is used.
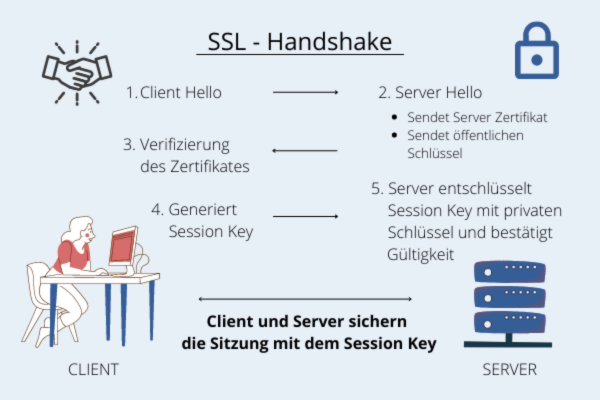
How exactly does it work?
SSL certificates verify online identity and consist of a key pair and verified identification data. Certificates can be requested from a certification authority.
During a connection, the identity of the web server is requested, so a copy of the SSL certificate is sent to the requesting browser.
After the browser verifies the trustworthiness, the server can send back a digitally signed confirmation. If everything matches, an SSL-encrypted session can now be established.
This process is called an “SSL handshake.”
AES-256-bit encryption
The AES method is a symmetric encryption scheme, meaning only one key is used.
AES is a block cipher whose block size depends on the key length. The length is therefore available in 128, 192, and 256 bits.
The predecessor DES (“Data Encryption Standard”) was replaced by AES (“Advanced Encryption Standard”) due to its short key length of 56 bits. As computer processing power increased, DES could no longer guarantee sufficient security.
The special feature of this encryption technology is the transformation that is applied to each block.
Example
The 4 encryption rounds
The encryption uses four different methods to transform the blocks. These methods are applied repeatedly in multiple successive rounds.
1. Substitution method
Each byte is encrypted using a substitution box—here, a rule is defined that determines which value a byte is replaced with.
2. Shift Row
The rows of the table are shifted to the right by a certain number of columns—the overflowing cells are appended on the left.
3. Mix Column
The columns are multiplied by a specific matrix—the bytes are not treated as numbers, but as polynomials.
4. Key Addition
Each block is linked with the current round key using XOR—the XOR operation is performed bit by bit.
This method is used in various areas, including data transmission via Wi-Fi or VPNs, as well as general data transfer.

Test leitzcloud now as a secure cloud solution
Secure your data in a securely encrypted cloud, with a sustainable data center in Germany.
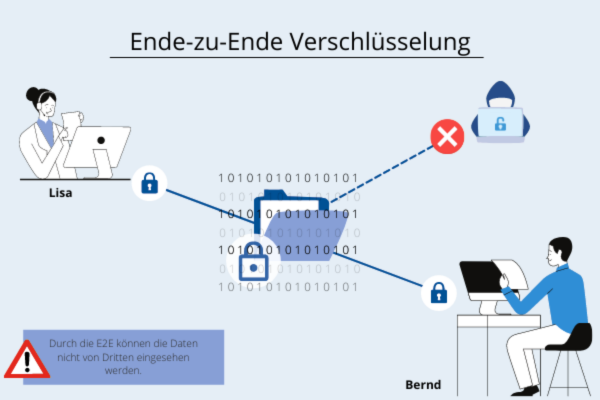
End-to-end encryption
= also referred to as “end-to-end encryption”
End-to-end encryption fully encrypts the data between sender and recipient and can only be decrypted using the intended recipient’s key. Encryption and decryption therefore take place exclusively at the endpoints of the transmission.
How exactly does it work?
With end-to-end encryption (E2EE), multiple encryption methods are used, so hybrid encryption is typically employed for the key exchange.
The transmitted data is encoded using symmetric AES-256 encryption and additionally authenticated at the communication endpoints through a digital SSL certificate.
For even greater security, a digital signature can be added to the encryption to verify access authorization.
Advantages
End-to-end encryption (E2EE) enhances data protection, as there is no access to personal data and it simultaneously prevents unauthorized access to data exchange.
Additionally, it is a tamper-proof method, as the key that grants access is only known to the sender and the recipient.